
Dipping your toes into DeFi can feel like an exciting, high-stakes game. But how do you actually manage the risks that come with it? The heart of managing DeFi smart contract risk really boils down to a three-part playbook: knowing what can go wrong, having solid defenses in place, and using modern tools to see trouble coming.
A Modern Approach to DeFi Risk Management
I like to think of DeFi investing as deep-sea exploration. To explore safely and actually find the treasure, you need a few things. You can't just dive in. You need a map of known hazards (that's your risk knowledge), a seriously reinforced submersible (your defensive strategies), and some advanced sonar to spot things in the dark (your monitoring tools). This framework cuts through all the noise and gives you a clear way to protect your capital.
This guide is built on that exact idea. We’ll give you actionable insights to help you secure your funds in the wild, fast-moving world of decentralized finance.
First, let's break down the core components of a solid risk management strategy. It's not about finding one silver bullet. Instead, it's about building a tough, resilient system with several layers of protection that overlap. We can think of these as the three pillars of modern DeFi risk defense.
The Three Pillars of DeFi Risk Management
Here’s a quick summary of the three pillars we'll be diving into.
Pillar | Description | Key Focus Area |
|---|---|---|
Knowledge (The Map) | Understanding the different ways things can go wrong, from code bugs to economic exploits. | Identifying and categorizing smart contract vulnerabilities. |
Defense (The Submersible) | Proactively setting up shields and safety nets to protect your capital before an attack happens. | Audits, timelocks, multi-sigs, insurance, and diversification. |
Monitoring (The Sonar) | Keeping a constant watch on your investments for emerging threats in real-time. | On-chain activity, governance proposals, and social sentiment. |
A truly effective approach is all about being proactive, not reactive. You need to build a system that expects things to fail and has a plan, rather than just cleaning up the mess after an exploit.
The big shift in mindset for seasoned DeFi investors is moving from being reactive to proactive. It's about building a system that anticipates where things could break, rather than just waiting to get hit by a preventable loss.
This multi-layered view is critical because attackers are always finding new ways to break things. If your strategy just relies on checking for a pre-launch audit, you're missing the entire world of risks that pop up after deployment, like oracle manipulation or governance takeovers. For a deeper dive on this, our guide on on-chain risk management has some great perspectives. When you bring all three pillars together, you create a framework that can actually adapt to new threats as they appear.
In this guide, we'll walk through each of these pillars in detail, moving from the theory to practical, real-world application. We'll start by breaking down the key risk categories you absolutely need to know, look at some famous exploits, and then give you a defensive playbook to protect your capital.
Unpacking the Critical DeFi Risk Categories
To get a handle on managing DeFi risk, you first have to know what you're up against. The threats aren't a single, monolithic problem; they're a collection of distinct vulnerabilities. Thinking of smart contract risk as one big scary thing is like thinking all illnesses are the same—it’s just not an effective way to protect yourself. Instead, we need to break it down.
This process is a bit like a doctor diagnosing a patient. You have to look at specific symptoms to figure out the underlying cause. In DeFi, this means categorizing risks so you can apply the right defensive medicine. The image below simplifies this whole approach into three core activities: building knowledge, deploying defenses, and actively monitoring.
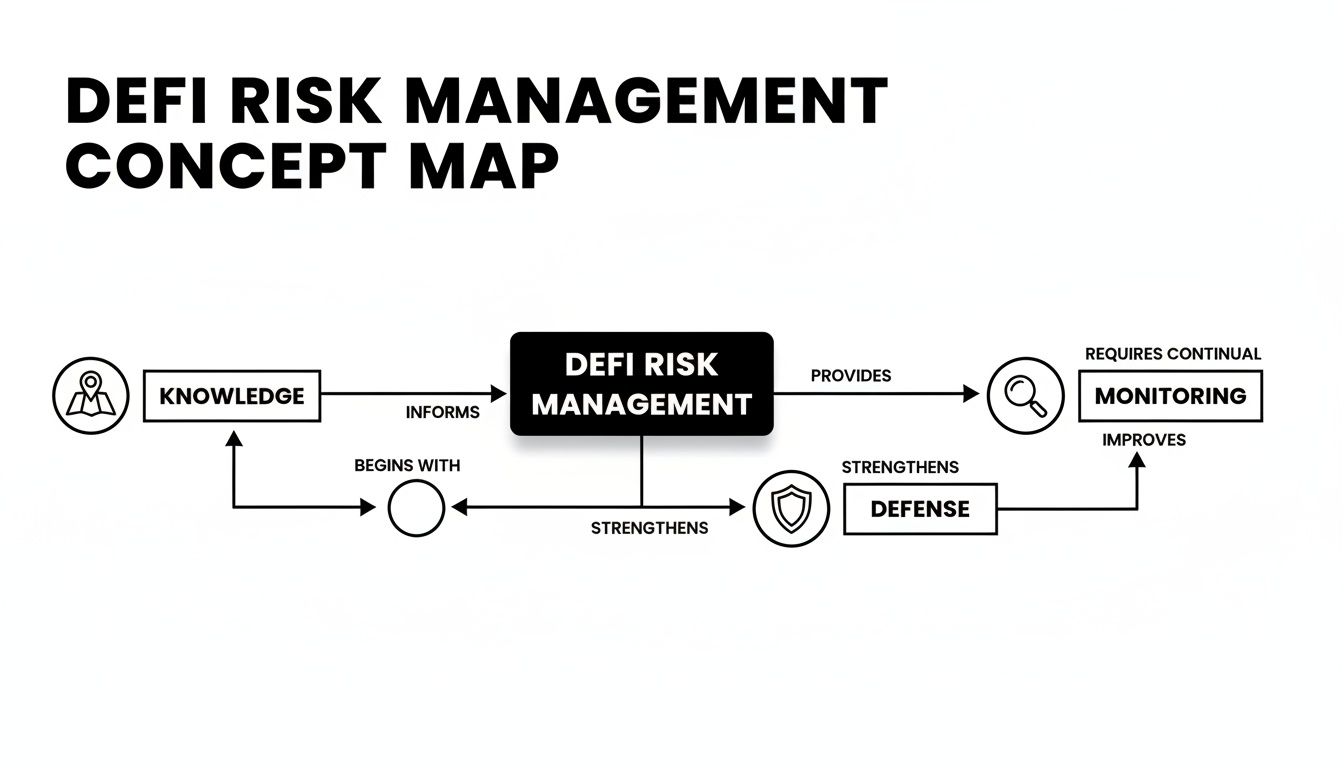
As you can see, effective risk management is a continuous cycle. Your knowledge informs your defenses, and constant monitoring tells you if those defenses are actually working. Let's start by building that crucial knowledge base.
Code Bugs and Logic Flaws
The most straightforward risk is a simple mistake in the code. Smart contracts are just programs, and like any software, they can have bugs. These can range from a minor typo to a critical logic error that lets an attacker drain every last penny from the protocol.
Imagine a bank vault where the blueprint has a mistake: one of the lock's tumblers is listed with the wrong number. Anyone who finds this flaw can craft a key to open it instantly. This is pretty much what happens with a reentrancy attack, one of the most infamous and costly bugs in DeFi history.
These are the kinds of vulnerabilities security audits are designed to find. But no audit is a 100% guarantee, and hackers are always discovering new, more subtle bugs. If you want to dive deeper into how protocols are evaluated for these flaws, check out our guide on smart contract risk scoring.
Economic and Design Flaws
Some risks aren't bugs in the code but weaknesses in the economic design of the protocol itself. The code might work exactly as intended, but an attacker finds a way to manipulate the system's financial logic for their own profit.
Think of it like a vending machine that sells sodas for $1. The code is perfect. But a clever user discovers they can insert a foreign coin that the machine thinks is worth $2, getting a soda and real change back for a worthless piece of metal.
A classic example in DeFi is a flash loan attack. Attackers borrow millions of dollars with zero collateral (for the span of a single transaction), use that capital to manipulate an asset's price on a decentralized exchange, and then exploit a lending protocol that relies on that manipulated price. The code didn't break; the economic model did.
Oracle and External Dependency Risk
Many DeFi protocols rely on external data sources called oracles to function. These oracles feed them crucial information like asset prices, which are needed to determine collateral values, trigger liquidations, and set swap rates. If this external data is wrong, the protocol can make catastrophic decisions.
This is like a stock market ticker suddenly reporting that Apple's stock is worth $0.01. Automated trading systems that trust this data would immediately sell, causing absolute chaos. If an oracle is compromised or just provides bad data, it can trigger unfair liquidations or let attackers borrow millions against worthless collateral.
A protocol is only as secure as its weakest dependency. If it relies on a single, centralized oracle for its price feeds, that oracle becomes a massive single point of failure.
Admin and Centralization Risk
While DeFi strives for decentralization, many protocols start out with—or keep—some level of centralized control. This usually comes in the form of admin keys: special accounts that can upgrade smart contracts, change protocol fees, or even pause the entire system.
When these keys are held by a single person or a small group, it creates a huge risk. A malicious founder could perform a "rug pull" by draining the protocol's funds, or an attacker could steal the keys and take complete control. This is the DeFi equivalent of a bank manager having the only key to the main vault and deciding to walk out with everything inside.
Operational and Social Engineering Risks
This category of risk is often overlooked but is quickly becoming the most dominant. It has less to do with the code itself and more to do with the human and infrastructure layers supporting the protocol. This includes everything from a developer's laptop being hacked to sophisticated phishing schemes that trick team members into revealing private keys.
Recent data shows a dramatic shift in where attackers are focusing. In 2023, a stunning $2.61 billion was stolen from the crypto space, but 78% of these losses were not from smart contract bugs. Instead, they came from infrastructure attacks targeting private keys, seed phrases, and privileged access. You can find more details in a recent crypto crime report, which highlights how attackers are moving up the stack from code to people.
Lessons From Real-World DeFi Exploits
It’s one thing to talk about risk in theory, but it’s a whole other ball game to see how these risks actually blow up in the real world. DeFi's history is unfortunately full of expensive lessons that double as perfect case studies for anyone trying to get a handle on managing DeFi smart contract risk. If we look past the shocking headlines, we can pick apart these incidents to see exactly where things went wrong and how to avoid similar disasters.
These aren't just technical glitches; they have very real, and often devastating, financial consequences. The image below of a broken digital bridge is a powerful metaphor for what happens when the core infrastructure we rely on in DeFi gives way.

This picture really hits home, showing the total collapse that happens during a bridge exploit. Value just seems to evaporate into thin air. Let’s dig into how something like this actually happens.
Case Study 1: The Cross-Chain Bridge Private Key Compromise
Cross-chain bridges, the protocols that let you move assets between blockchains, are incredibly complex and have a ton of potential weak spots. Because they secure massive amounts of capital, they’ve always been a juicy target for attackers.
A classic example involved a bridge’s validator network—the group supposed to confirm transactions moving between the two chains. In one massive hack, attackers managed to get their hands on the private keys for enough of these validators to take control. This gave them the power to approve a completely fraudulent withdrawal. They basically minted assets on one chain without locking up the real assets on the other, then walked away with millions.
This left the bridge completely undercollateralized and its users holding what were essentially worthless IOUs.
The big lesson here is that “decentralization” on paper means nothing. If an attacker can compromise just a handful of key-holders to seize control, the system is basically centralized and extremely fragile.
This incident wasn't about a bug in the code itself, but a massive failure in operational security—specifically, how the privileged keys controlling the protocol were managed. This is a trend that's only gotten worse. In just three months of 2026, hacks targeting cross-chain bridges and related protocols topped $137 million.
Case Study 2: The Flash Loan Economic Exploit
Not all hacks come from sneaky code bugs. Some of the most creative—and destructive—exploits manipulate a protocol’s basic economic rules. Flash loan attacks are the perfect example of this.
Flash loans let a user borrow millions of dollars with absolutely zero collateral, but only for the duration of a single, atomic transaction. If the loan isn't paid back by the end of that transaction, the whole thing just reverses as if it never happened.
Here's how an attacker turns this into a weapon:
The Loan: The attacker borrows a huge amount of an asset, like millions in ETH, using a flash loan.
The Manipulation: They dump this capital onto a decentralized exchange (DEX) that has low liquidity for a specific token, causing a massive, temporary price spike.
The Exploit: Next, they turn to a separate lending protocol that happens to use that same DEX as its price feed. Seeing the artificially jacked-up price, the lending protocol thinks the attacker's collateral is worth a fortune and lets them borrow a huge amount of other assets against it.
The Getaway: In the final step, the attacker repays the original flash loan and pockets the difference they drained from the second protocol. All in one transaction.
In this scenario, the lending protocol's code worked exactly as intended. The fatal flaw was in its design: it relied on a single, easily manipulated price feed. It's a stark reminder of why using robust, manipulation-resistant oracles is non-negotiable. It’s useful to think about these vulnerabilities in the same way the web development world thinks about the OWASP Top 10, a list of the most critical security flaws in traditional web apps.
By studying these real-world failures, we can arm ourselves with a much smarter defensive strategy. Our guide on https://yieldseeker.xyz/blog/protocol-safety-analysis gives you a solid framework for applying these lessons when you're sizing up your next DeFi investment.
Your Defensive Playbook for Staying Safe

Alright, we've talked about all the things that can go wrong. Now for the important part: what you can actually do about it. Knowing the risks is one thing, but building a solid defense is how you survive and thrive in DeFi.
Think of this section as your practical guide. We’re going to walk through the tools and tactics that put a shield around your crypto, shifting you from a potential victim to someone who’s actively in control of their own security.
The First Line of Defense: Security Audits
A smart contract audit is your absolute first stop. Think of it like getting a professional inspection before you buy a house. Experts tear through the code line-by-line, hunting for common bugs, logic flaws, and any other weaknesses before a protocol is unleashed on the world.
But here’s the thing: an audit is not a magic shield that guarantees 100% safety. It's just a snapshot in time. A good audit is crucial, but it's not the end of the story.
Keep these points in mind when you see that "audited" badge:
Scope Matters: Did the audit cover the entire protocol, or just a few core contracts? Sometimes teams only get the main parts audited, leaving other areas exposed.
Who Did the Audit?: Not all auditors are created equal. You want to see reports from well-known firms with a track record of finding critical bugs.
Code Changes Everything: An audit is only good for the code that was actually reviewed. If the team pushes updates after the audit, those changes introduce brand new, unaudited risk.
A passed audit is a great start, but it’s just one piece of a much larger puzzle.
The Gold Standard: Formal Verification
For protocols that absolutely cannot fail, some teams go a step beyond audits to formal verification. This is a whole different beast. It's a deeply mathematical process where you don't just look for bugs—you try to prove that the code works perfectly.
Formal verification aims to prove, with mathematical certainty, that a contract’s code behaves exactly as intended under all possible conditions. It's like proving a geometric theorem rather than just measuring the angles.
This method can wipe out whole categories of bugs, which is why it’s considered the gold standard. The catch? It’s incredibly expensive, slow, and requires a ton of specialized brainpower, so you won’t see it on every project. To build truly resilient smart contracts, however, implementing robust secure coding practices from the very beginning is a must.
On-Chain Guardrails: Multisigs and Timelocks
The best protocols build safety measures right into their DNA. Two of the most important tools here are multisigs and timelocks, which act like circuit breakers to prevent disaster.
A multisig (multi-signature) wallet means that no single person has the keys to the kingdom. Instead, it requires multiple people to approve a transaction before it goes through. For example, a 3-of-5 multisig requires at least three out of five designated keyholders to agree on any change. This stops a single rogue dev or a hacker with one stolen key from draining the treasury.
A timelock forces a mandatory delay—a "cooling-off period"—before any major change can take effect. Whether it's a code upgrade or a change in fees, this delay gives the community a heads-up. It provides time for everyone to review the change, spot anything fishy, and pull their funds out if they don't like what they see.
These aren't just nice-to-haves; they are essential for managing admin risk and keeping power in check.
Your Personal Lines of Defense
Even with all the protocol-level safety, a few final layers of defense rest with you.
DeFi Insurance: Services like Nexus Mutual let you buy coverage on specific smart contracts. If a protocol you're using gets hacked and you've got a policy, you can file a claim to get your money back. It's a direct way to hedge against code risk.
Personal Security: The human element is often the weakest link. Always be on guard for phishing scams, use a hardware wallet for your serious crypto holdings, and regularly revoke token approvals you don't need. Your own security habits are a critical firewall.
By layering these strategies—from checking for audits and on-chain safeguards to using insurance and practicing good personal security—you can build a formidable defense. This is how you go about managing DeFi smart contract risk like a pro and make much smarter decisions in this space.
Automating Your Defenses With AI-Powered Tools
Let's be honest: manually staying on top of every risk in DeFi—from code updates to market sentiment—can feel like a full-time job. The defensive strategies we've covered are powerful, but they all depend on constant vigilance. That’s something few of us actually have the time to maintain.
This is where AI-powered platforms are starting to make a real difference.
Services like Yield Seeker are built to do the heavy lifting of managing DeFi smart contract risk. Think of it like having a personal risk analyst working for you 24/7, tirelessly scanning the on-chain world for anything that looks out of place.
These tools aren't just looking at old news or yesterday's audit reports. They are actively monitoring the live environment, hunting for emerging threats that could put your capital at risk before they blow up.
The Power of Real-Time Monitoring and Response
Old-school risk management usually means periodic checks—maybe you review an audit or check a dashboard once a week. In DeFi, that’s an eternity. A protocol can go from perfectly safe to completely drained in minutes. AI-powered tools close this critical gap.
This automated monitoring and response cycle is what sets them apart:
Continuous Threat Detection: The AI models are always working, analyzing on-chain data, social media chatter, and governance proposals to spot red flags long before they turn into a full-blown crisis.
Automated Capital Allocation: When a potential threat pops up in one protocol, the system can automatically shift your capital to safer, pre-vetted alternatives. You don't have to lift a finger.
Risk-Adjusted Yield Optimization: The goal isn't just chasing the highest number on a dashboard; it's about finding the best risk-adjusted yield. These AI agents are constantly balancing the potential for high returns against a protocol's real-time security.
This kind of automated defense system makes sophisticated risk management accessible to everyone, from busy professionals to people just getting their feet wet in DeFi.
By automating the research, monitoring, and execution loop, AI tools are making safer DeFi yields available to everyone. It turns a complex, time-consuming grind into a simple, hands-off experience.
User Experience as a Core Safety Feature
These days, modern risk management is about more than just fancy backend systems. You'd be surprised how much user-centric design plays a role in keeping you safe. Confusing interfaces and restrictive terms can introduce their own set of risks.
Features that might seem like simple conveniences are actually vital parts of a modern risk strategy:
No Lockup Periods: The ability to withdraw your funds at any time is a massive risk mitigation tool. If you spot trouble or just need your money back, you shouldn't be trapped by arbitrary lockups.
Simple, Clear Interfaces: A clean dashboard that shows your balance, earnings, and where your money is at a glance removes all the guesswork. It helps you make informed decisions quickly, without getting lost in a sea of data.
Effortless Execution: Platforms like Yield Seeker let you deposit funds with a few clicks and let the AI handle the rest. This simplicity cuts down on the chance of user error—a surprisingly common way people lose funds.
Ultimately, these tools are built to handle the immense complexity of DeFi for you. They let you tap into the ecosystem's opportunities without needing to become an expert in smart contract auditing or on-chain data analysis yourself.
Common Questions on DeFi Risk
Even after you've got a solid plan, DeFi can still throw some curveballs. It's a space that moves at lightning speed, and it's not always easy to tell a smart investment from a disaster waiting to happen. This section dives into the most common and practical questions we get about managing smart contract risk.
The idea here is to cut through the jargon, clear up a few common myths, and help you navigate the DeFi world with a bit more confidence. Let's tackle some of those lingering concerns you might have.
Is a Security Audit a Guarantee of Safety?
This is probably one of the biggest misunderstandings in all of DeFi. Getting a security audit from a well-known firm is an absolute must-have for any serious protocol, but it is not a 100% guarantee of safety. Think of it more like a home inspection before you buy a house—it's great for spotting existing issues but can't predict what might go wrong in the future.
Here’s a quick rundown of what an audit simply can't cover:
Future Code Changes: An audit is just a snapshot in time. Any code that gets updated or changed after the audit is finished is completely unaudited and introduces brand new, unknown risks.
Economic or Design Flaws: Most auditors are hunting for specific code bugs like reentrancy vulnerabilities. They might totally miss clever economic exploits where the code works perfectly but the underlying financial logic can be gamed.
Rug Pulls and Malicious Insiders: An audit can't read minds or tell you if a team is trustworthy. If the developers hold powerful admin keys that can drain the contracts, an audit won't stop them from using them.
An audit is a vital piece of due diligence, but it should be the start of your research, not the end of it.
How Can I Tell if a Protocol Is Truly Decentralized?
"Decentralization" is a term that gets thrown around a lot in crypto, and honestly, it's often misunderstood. So many protocols claim to be decentralized but still have single points of failure that could bring everything down. The truth is, decentralization is a spectrum, not a simple yes-or-no question.
A quick way to get a feel for a protocol's decentralization is to check for on-chain rules that limit what any one person or group can do.
A key sign of genuine decentralization is the use of timelocks and multi-signature wallets to control important functions. If a protocol can be changed or shut down instantly by a single wallet, it’s not really decentralized in any meaningful way.
Ask yourself these questions when you're looking at a project:
Who holds the admin keys? Is control in the hands of a multisig that requires several independent people to sign off on changes?
Is there a timelock? Do major protocol changes have a mandatory waiting period, giving everyone a chance to review what's happening and pull their funds if they don't like it?
Is the governance process real? Does the community actually get a say in proposals, or is it just a few whales and insiders calling all the shots?
If you can't find clear, good answers to these questions, you’re probably looking at a project with a much higher degree of centralization risk.
What’s the Single Biggest Risk I Should Worry About Today?
While crazy new code exploits grab all the headlines, the data points to a different trend: the biggest and most expensive hacks are increasingly about operational security and private key management.
In 2024 alone, over $1.5 billion has been lost to hacks and exploits. But a massive chunk of that didn't come from some genius new coding attack. It came from old-school security screw-ups like:
Stolen private keys from a developer or a validator.
Sophisticated phishing attacks that tricked team members.
Compromised third-party tools that a protocol was depending on.
This means that while you absolutely need to care about a protocol's code, you also have to think about how competent the team is at basic security. A project can have perfect code and still get drained because a developer got sloppy and clicked a bad link.
Can DeFi Insurance Really Protect Me?
Yes, DeFi insurance can be a fantastic tool, but you've got to know what you're buying. Services like Nexus Mutual let you buy coverage for a specific protocol against a specific risk, which is most often a smart contract bug leading to a loss of funds.
If you buy a policy on a lending protocol and it gets hacked because of a flaw in the code, you can file a claim to get your money back. But there are some catches:
Coverage is specific: Your policy will only cover exactly what it says it covers. It probably won't help you if there's an oracle failure or the team decides to rug pull.
Claims aren't guaranteed: Claims are usually put to a vote by the insurance protocol's own members. They'll look at what happened and decide if it matches your policy's terms. It's possible your claim could be denied.
Capacity can be limited: For really popular protocols, all the available insurance might already be sold out, meaning you can't get coverage even if you want it.
Even with those caveats, buying insurance is a direct and smart way to hedge against smart contract risk, especially for your biggest positions. It’s a key part of building a layered defense for your portfolio.
Manually tracking protocols, analyzing risks, and moving funds is a constant battle. Yield Seeker automates this entire process. Our AI-powered platform continuously monitors the DeFi landscape for you, automatically allocating your stablecoins to opportunities that meet our strict risk criteria. Stop spending hours on research and start earning smarter, safer yield today at yieldseeker.xyz.