

Smart contract monitoring is basically a 24/7 security guard for your DeFi investments. It's constantly watching a contract’s real-time behavior for any signs of trouble. This isn't about catching exploits after your funds are gone; it's about spotting the shady activity before the damage is done.
Your Digital Watchtower for DeFi Assets
Think about it like this: a smart contract audit is like getting the blueprints for a high-tech bank vault checked for flaws before it’s built. It’s a crucial first step.
But smart contract monitoring is the live security system you install after the vault is built and filled with millions in user funds on chains like Base. It’s the network of motion detectors, pressure plates, and thermal sensors that watch every single interaction once the vault is up and running. This system doesn't just wait for a loud explosion; it flags the subtle stuff, like a faint tremor near a wall or an unusual temperature spike, that hints at a threat taking shape.
In DeFi, this means keeping an eye on every transaction, function call, and data flow in real time. For anyone holding stablecoins to earn passive income, this constant vigilance is what stands between you and a potential disaster. The whole point is to shift from cleaning up a mess to preventing one in the first place, giving everyone a heads-up to act before things get ugly.
Why This Matters More Than Ever
The need for solid monitoring is exploding right alongside the smart contract market itself. We're looking at a market projected to leap from $3.39 billion in 2026 to a staggering $16.31 billion by 2034. That's a blistering growth rate of 26.30% every year. If you want to dig into the numbers, you can explore the full market analysis here.
All that growth means way more value is getting locked into DeFi protocols, making them bigger and juicier targets for attackers. With so much more on the line, automated solutions aren't just a "nice-to-have" anymore; they're essential.
For the average stablecoin holder, this boils down to three huge wins:
Asset Protection: It’s a powerful shield against the hacks and exploits we hear about all too often.
Less Hassle: Automated systems, like the AI agents we're building at Yield Seeker, take the soul-crushing work of manually tracking protocol health off your plate.
Peace of Mind: You can make smarter decisions knowing your capital has a constant, watchful eye on risk.
Smart contract monitoring is the difference between having a simple lock on your door and having a full-blown security system with live alerts. One stops a casual attempt; the other actively defends against someone determined to get in.
What a Modern Monitoring System Actually Watches
A top-notch monitoring strategy does more than just watch transactions go by. It’s about keeping tabs on several key areas to make sure a DeFi protocol is healthy and safe. For investors, knowing what a secure platform should be looking at is half the battle. A great system gives you a clear window into a protocol’s health, which is absolutely critical if you're trying to earn yield safely.
To give you a clearer picture, here’s a quick rundown of the most important things a monitoring system needs to cover.
Key Monitoring Areas for DeFi Investors
Monitoring Area | Why It's Critical | Example Risk |
|---|---|---|
Transaction Volume & Flow | Sudden spikes or drops in transaction activity can signal a coordinated attack, a flash loan exploit, or a bank run in progress. | An attacker uses a flash loan to manipulate a protocol's oracle, causing a massive, unusual spike in transaction volume just before draining funds. |
Oracle & Price Feeds | Oracles connect smart contracts to real-world data like asset prices. If they are manipulated, the protocol can be tricked into making bad decisions. | A faulty or manipulated price feed could make a protocol think an asset is worthless, allowing an attacker to drain liquidity pools at a massive discount. |
Governance & Admin Actions | Malicious changes to a protocol’s rules or parameters by a compromised admin key are a common attack vector. | A hacker gains control of an admin key and changes the withdrawal fee to 100%, effectively trapping all user funds. |
Liquidity & Collateral | Monitoring the health of liquidity pools and collateral ratios is key to preventing insolvency or cascading liquidations. | A sharp drop in the value of a major collateral asset could trigger a wave of under-collateralized loans, putting the entire protocol at risk. |
Ultimately, keeping an eye on these areas is what separates a safe, reliable DeFi protocol from a ticking time bomb. It's about building a complete picture of a protocol's health, not just looking at one piece of the puzzle.
How a Modern Monitoring System Works
To really get what smart contract monitoring is all about, it helps to look under the hood. It’s not just one tool, but a system of layers working together—kind of like a high-tech home security setup built to protect your most valuable stuff. Each layer has a specific job, building on the last to create a complete defense.
This layered approach is the key to moving from just reacting to problems to actively defending against them. The system is always watching on-chain activity, mixing different analysis methods to catch high-risk transactions before they can do any damage. Let's break down how it all fits together.
Layer 1: The Data Collection Layer
The foundation of any good monitoring system is its ability to see everything. That’s the job of the Data Collection Layer. Its only purpose is to grab raw, unfiltered information straight from the blockchain.
Think of this layer like the sensors in a home security system—the motion detectors, window sensors, and cameras. They don't make judgments; they just watch and report what’s happening. In the same way, this layer connects to blockchain nodes to pull in a constant stream of data, including:
Transactions: Every single transaction sent to or from the contract you're watching.
Events: Specific logs the smart contract emits to signal that certain actions took place.
State Changes: Any change to the contract's internal data, like an account balance changing or an admin setting getting updated.
Function Calls: The specific functions being run inside the contract.
This raw data is the lifeblood of the whole system. Without it, the other layers are just flying blind.
This diagram shows the core pieces that a monitoring system's data layer tracks to protect a digital vault.
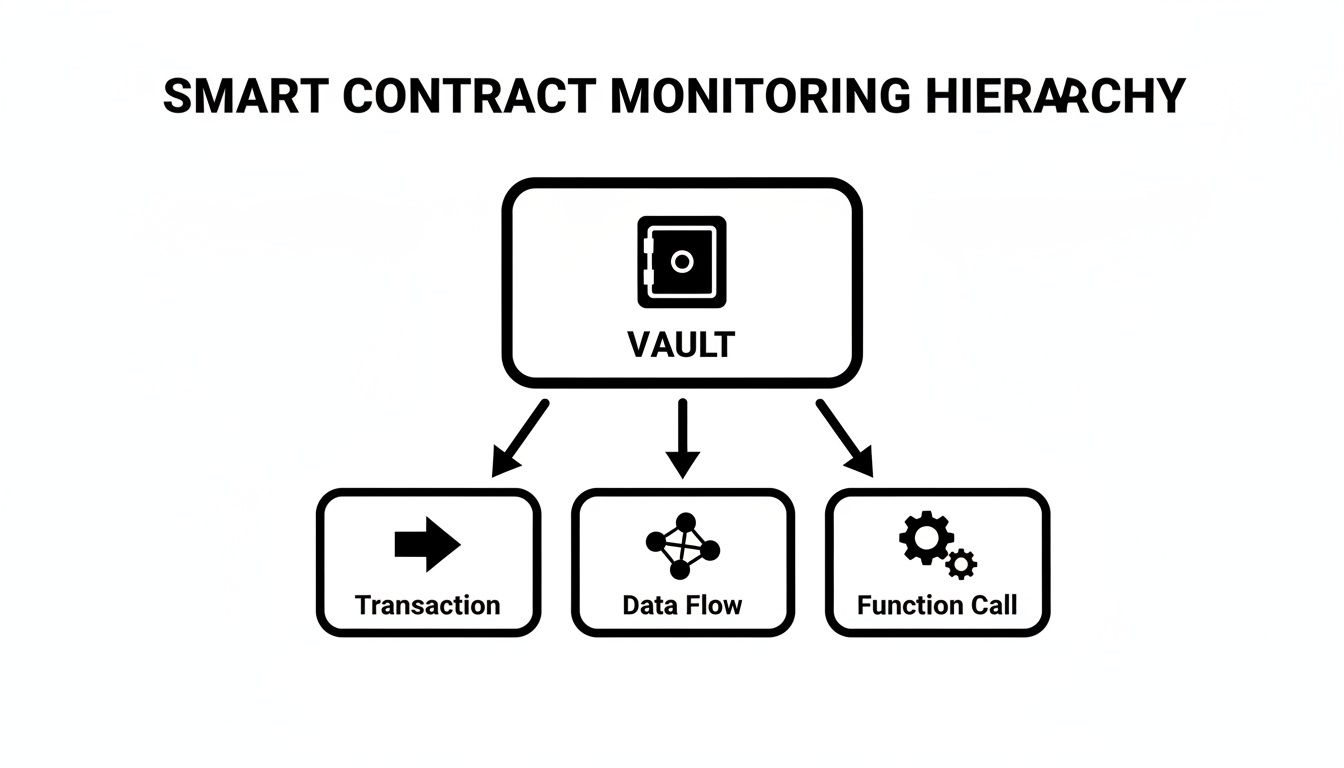
As you can see, monitoring starts with the vault’s core components—transactions, data flows, and function calls—which provide the raw material for security analysis.
Layer 2: The Processing Layer
Once all that raw data is collected, it needs to be organized and made sense of. That’s where the Processing Layer comes in. It’s like the central hub of the security system, taking all the raw feeds from the sensors and putting them into a format that’s easy to analyze.
This layer decodes complicated transaction data, sorts events into categories, and adds helpful context. For example, it might figure out which address started a transaction, how much money was moved, and which exact protocol function was used. It basically turns a chaotic firehose of blockchain data into a clean, easy-to-read story of what’s happening.
Layer 3: The Analysis Layer
This is where the real magic happens. The Analysis Layer is the brain of the whole operation. It takes the processed data and starts looking for suspicious patterns, weird anomalies, or the tell-tale signs of known attacks.
This layer is what separates a simple notification tool from a true smart contract monitoring solution. It’s the difference between a smoke detector that just beeps loudly and an advanced system that can tell you if it's burnt toast or a real fire.
The best systems use a mix of methods here:
Rule-Based Engines: These use pre-set rules to flag specific, known-bad activities. For example, "Alert me if an admin key that hasn't been used in six months suddenly becomes active."
Behavioral Analytics: This is all about learning what "normal" activity looks like for a contract. Once a baseline is set, the system can flag anything that strays too far from it.
Machine Learning Models: AI can spot new and complex attack patterns that simple rules would miss. It learns from huge datasets of both good and bad on-chain activity to get smarter over time.
Layer 4: The Alerting Layer
Finally, when the Analysis Layer spots a real threat, the Alerting Layer jumps into action. This is the alarm bell. Its job is to get a notification to the right people through the right channels so they can respond immediately.
This isn’t just about sending a generic email. A good alerting layer plugs directly into a team's day-to-day workflow, sending instant notifications to places like Slack, Discord, or Telegram. These alerts are built to be acted on, giving clear context on what the threat is, how bad it is, and where it’s happening. This empowers teams to jump on the situation and stop any potential damage before it gets out of hand.
Key Signals and Metrics to Watch

Smart contract monitoring isn’t about watching everything. That’s just a firehose of useless data. Effective monitoring is about watching the right things—the specific signals that act as your personal early warning system.
Think of it like a pilot's cockpit dashboard. They aren't staring at every single mechanical detail of the plane. They’re focused on the critical metrics: altitude, airspeed, engine temp. These give a clear, immediate picture of the aircraft's health. In DeFi, our dashboards do the same, highlighting trouble long before it becomes a full-blown crisis.
These signals really fall into three buckets: financial, security, and operational. Each gives you a different lens to look through, and by watching all three, you build a much stronger defense with far fewer blind spots for attackers to sneak through.
Financial Signals
Financial signals are the most direct pulse-check on a protocol's economic health. They track the flow of money and the stability of the assets locked inside the smart contracts. A sudden, weird change here is often the very first sign of an exploit or a rug pull kicking off.
Here are the big ones to watch:
Sudden Liquidity Drains: A huge, rapid withdrawal from a liquidity pool is a massive red flag. This could be an insider getting ready to bolt or an attacker who's found a way to bleed the protocol's reserves dry. Look at the $182 million Beanstalk Farms exploit—it started with a flash loan that manipulated governance, giving the attacker a green light to drain everything.
Unusual Price Volatility: Yeah, crypto is volatile, but monitoring systems are trained to spot price moves that just don't make sense. A sudden, isolated crash in one specific token inside a protocol could mean a compromised price oracle, which has been the weak link in countless DeFi hacks.
High Volume of Small, Rapid Trades: This pattern can sometimes be a setup. An attacker might be trying to manipulate an asset's price on a decentralized exchange, often as the first step in a much more complex attack.
Security Signals
Security signals are all about the technical and admin side of the smart contract itself. These alerts are designed to catch anything that deviates from normal behavior or suggests someone unauthorized has grabbed the keys to the kingdom. If you want to go deeper on this, check out our guide on smart contract risk scoring.
Keep an eye out for these security signals:
Unauthorized Contract Upgrades: If a contract can be upgraded, any change coming from an address that isn't the official multi-sig or governance contract is a sign of a potential takeover. Simple as that.
Suspicious Function Calls: You can set up alerts for sensitive functions like
setAdmin()ortransferOwnership(). If a call comes from an unexpected address, you can catch a private key compromise before it turns into a disaster.Flash Loan Attack Patterns: These attacks are lightning-fast, often happening in a single block. But they follow a specific sequence of transactions. Good monitoring can spot these patterns as they unfold, giving you a chance to react.
Operational Signals
Operational signals are about the health of the protocol's plumbing and infrastructure. These issues might not be malicious, but they can definitely put user funds at risk if they aren't addressed.
Here are a few common operational tripwires:
Oracle Failures or Delays: Oracles are the bridge between the blockchain and real-world data. If a price feed goes down or starts feeding bad data, it can trigger wrongful liquidations and open the door for nasty arbitrage attacks.
Excessive Network Congestion: While not a direct hack, a clogged network can be just as dangerous. It can stop you from topping up collateral to avoid getting liquidated during a market dip, which is a terrible feeling.
Critical Monitoring Signals by Category
To tie this all together, here’s a quick look at the kinds of threats these signals help you catch. Effective systems track a blend of these to create a comprehensive safety net.
Signal Category | Example Signal | Potential Threat |
|---|---|---|
Financial | Large, rapid withdrawal from a liquidity pool. | Exploit in progress or an insider rug pull. |
Financial | Sudden price drop in one asset, against market. | Price oracle manipulation or a targeted token dump. |
Security |
| Compromised private keys or an administrative takeover. |
Security | Contract code is updated outside of governance. | Unauthorized and potentially malicious upgrade. |
Operational | Price feed oracle hasn't updated in 15 mins. | Risk of incorrect liquidations or arbitrage attacks. |
Operational | Gas fees spike by 500% on the network. | Inability to manage positions or prevent liquidation. |
By keeping tabs on these varied signals, you're not just watching your assets; you're actively defending them from a wide range of potential disasters. This holistic view is what separates a reactive approach from a truly proactive one.
Building Your Monitoring and Response Plan
Knowing which signals to watch is only half the battle. The real work is turning that knowledge into a concrete plan that actually protects your assets. A solid smart contract monitoring strategy isn’t just about setting up alerts; it's about building a complete system that connects detection directly to action.
This is how you transform monitoring from a passive chore into a proactive defense. For Web3 teams, it’s a non-negotiable part of risk management. For individual investors, understanding this process shows you what level of preparedness you should expect from the platforms you trust with your money.
Identifying Your Critical Assets
First things first: you need to map out what you absolutely must protect. This goes way beyond just the main contract holding user funds. A thorough plan identifies every critical component that, if compromised, could spell disaster.
Your list of critical assets should include:
Core Treasury or Vault Contracts: This is the big one—the primary contracts holding the majority of user deposits or protocol funds.
Governance Contracts: These control protocol upgrades, parameter changes, and other admin functions. A hostile takeover here can be game over.
Price Oracles: The data feeds your protocol relies on for accurate asset pricing. A manipulated oracle can be just as devastating as a direct hack.
Admin Wallets: Any wallets or multi-sigs with special powers to pause contracts, change fees, or access emergency functions.
By defining these assets, you create a focused scope for your monitoring efforts. You're making sure you’re watching the doors that matter most.
Defining Alert Thresholds and Workflows
Once you know what to watch, the next step is to define what counts as "suspicious" activity. This means setting specific, actionable alert thresholds. Vague rules like "monitor for large withdrawals" are useless. You need to create precise triggers.
For example, a much better rule would be: "Alert immediately if more than 15% of the total liquidity is withdrawn from the main USDC pool within a single 10-minute window." This is specific, measurable, and directly tied to a potential risk.
Of course, an alert that nobody sees is worthless. Notifications need to be routed directly to on-call channels in Slack, Discord, or Telegram for immediate attention.
A well-defined alert is the difference between early detection and a painful post-mortem. It’s the tripwire that gives your team a fighting chance to contain a threat before it blows up.
When things do go wrong, having a clear strategy is everything. A comprehensive incident response playbook can provide the structure your team needs to act decisively when the pressure is on.
A Simple Incident Response Checklist
When an alert fires, chaos is the enemy. A simple, clear checklist ensures your response is logical and swift. While a full-blown plan can get complex, every team should start with these fundamentals.
Triage the Threat: First, confirm if the alert is a real threat or just a false positive. Is this an actual exploit in progress, or is it a scheduled, large-scale treasury movement? Verification is crucial to avoid hitting the panic button unnecessarily.
Contain the Damage: If the threat is real, the immediate priority is to stop the bleeding. This often means hitting a pre-planned "pause" function on the smart contract, which temporarily halts all withdrawals and sensitive transactions to prevent any more funds from draining out.
Communicate Clearly: Transparency is key. As soon as you have confirmed details, let your users and the wider community know what's happening. Be honest about what happened, what you're doing to fix it, and what they should expect next.
Resolve and Remediate: After containing the threat, the focus shifts to fixing the underlying vulnerability. This involves a deep dive into the code, patching the issue, and almost always getting a third-party review before you even think about un-pausing the protocol. You can learn more about this process in our guide to a proper smart contract security audit.
How AI Is Changing The Game for Smart Contract Monitoring

Most smart contract monitoring today is built on fixed, rule-based systems. Think of it like a classic home security alarm—it’s great at telling you when a window breaks, but it’s completely blind if a clever intruder finds another way inside. These systems can only spot threats they’ve been specifically programmed to look for.
This is where Artificial Intelligence (AI) and Machine Learning (ML) come in and completely flip the script. Instead of just working off a static checklist, AI-powered monitoring learns what "normal" looks like for a protocol and then flags anything that strays from that baseline. This shifts the entire approach from reactive defense to proactive protection.
It’s like upgrading from that simple alarm to a security guard with years of experience who just knows when something is off. This guard doesn't just watch for broken windows; they notice the car circling the block too many times or the person loitering across the street. AI does the same for smart contracts, but at a speed and scale no human team could ever hope to match.
Moving Beyond Static Rules
The real magic of an AI-driven system is that it doesn't need a pre-written rule to spot a new kind of threat. By training on huge datasets of both legitimate and malicious on-chain activity, it learns to recognize the signature of an attack, even if it’s a zero-day exploit that has never been seen before.
This is absolutely crucial in DeFi, where attackers are constantly cooking up new ways to drain protocols. A rule-based system is always playing catch-up, waiting for the next big hack before adding a new rule. An AI system, on the other hand, can spot the weird patterns of a brand-new attack as it’s happening.
AI transforms smart contract monitoring from a simple tripwire into an intelligent immune system. It doesn’t just respond to known threats; it identifies and isolates new, unforeseen infections before they can cause systemic damage.
This is a huge deal for catching complex financial attacks that might look like normal transactions when viewed one by one. An AI model can connect the dots across millions of data points at once to see the bigger picture of a coordinated exploit taking shape.
Predictive Analytics and Autonomous Defense
The true power of AI in smart contract monitoring comes down to its ability to predict what's coming next. By analyzing subtle shifts in on-chain data, AI models can forecast potential risks before they turn into full-blown crises. This is the core idea behind advanced platforms like Yield Seeker.
Our AI agents aren't just simple yield optimizers; they’re sophisticated risk managers at heart. They use predictive analytics to constantly check a protocol's health across dozens of different angles. If an agent detects that a protocol's risk profile is creeping up—maybe due to strange governance votes or suspicious token movements—it can autonomously move capital to safer, more stable ground.
This creates a layer of smart defense that you just can't get with manual monitoring. It brings some serious advantages:
Real-Time Anomaly Detection: AI can instantly spot tiny deviations in massive datasets that a human analyst would almost certainly miss.
Proactive Risk Mitigation: By predicting potential threats, AI can trigger defensive moves before an exploit happens, not after the damage is done.
Adaptive Learning: AI models are always learning from new data, getting smarter and better at catching emerging threats over time.
This hands-off capability is especially valuable for anyone looking to earn passive income on their stablecoins without needing to become a full-time security analyst. If you're curious how this all works under the hood, you can learn more about the tech behind an AI-driven DeFi agent and how it keeps your capital safe.
Ultimately, AI automates the constant vigilance needed to navigate DeFi safely, giving you both peace of mind and more resilient returns.
Your Shield in the World of DeFi
Throughout this guide, we've broken down smart contract monitoring from every angle. We started with the basics, picturing it as a digital watchtower, and then dug into its architecture, the signals that really matter, and how to build a solid response plan. What's clear is that this kind of constant vigilance isn't just a nice-to-have; it's a must for anyone serious about navigating DeFi safely.
The journey from simple, rule-based alerts to smart, AI-driven defense is a huge leap forward in how we protect our digital assets. This shift is key to making DeFi more secure and accessible for everyone, from big institutional treasuries to individuals holding stablecoins. Think of smart contract monitoring as your personal shield in a world full of risks.
The real goal here is to move from reactive panic to proactive protection. It's about giving you a transparent layer of security that works 24/7, so you can make smarter, more confident investment decisions.
Making Smarter Investment Choices
When you choose platforms with strong, automated monitoring, you’re doing more than just chasing returns—you're actively managing your risk. This is the whole idea behind solutions like Yield Seeker, where AI agents act as both yield finders and tireless risk managers. They handle the heavy lifting of continuous research and vigilance, something that's just not practical for most of us to do on our own.
This approach offers a straightforward way to earn on your stablecoins without the constant stress of watching the markets yourself. It makes automated systems an easy and transparent way to secure your capital.
At the end of the day, effective smart contract monitoring gives you the peace of mind to actually participate in DeFi with confidence. It means your assets aren't just out there working for you; they're also being actively defended, letting you focus on your financial goals while your shield stays up.
Common Questions
Diving into smart contract security can bring up a few questions. Let's tackle some of the most common ones to clear things up and show you how monitoring fits into protecting your DeFi assets.
So, Can Smart Contract Monitoring Prevent Every Single Hack?
Honestly, no. Anyone who tells you their security system is 100% foolproof isn't giving you the full picture. Smart contract monitoring is no different. It can't stop a completely new, never-before-seen zero-day exploit or a super complex economic flaw in its tracks.
But thinking of it purely as a prevention tool misses the point. Its real power is as an incredibly effective early-warning system.
Think of smart contract monitoring like an advanced seismic sensor. It won't stop the earthquake, but it gives you that critical heads-up to take cover before the real shaking starts. That warning can make all the difference.
By catching weird activity as it happens—like a sudden, massive liquidity drain or an admin key being used when it shouldn't be—it gives the team a crucial window to hit the panic button. This means they can pause contracts, blast out a community alert, and contain the problem before the funds are gone for good. So while it’s not an impenetrable shield, it dramatically cuts down the risk by turning a potential disaster into a fire drill.
What's the Difference Between Monitoring and an Audit?
This is a big one, and it's easy to get them mixed up. They both play a huge, but very different, role in keeping a protocol safe. The best analogy is thinking about an airplane's safety checks.
A smart contract audit is like the exhaustive, one-time inspection the plane gets before it even thinks about taking off. Engineers go through every single line of code, checking for structural weaknesses, bugs, and potential weak spots while the plane is safely on the ground. It's a static review of the code that's absolutely vital for a safe launch.
Smart contract monitoring, on the other hand, is the live dashboard in the cockpit after the plane is in the air. It's constantly tracking engine performance, altitude, and weather conditions in real-time. This protects the protocol while it's live, interacting with thousands of users and other protocols, and guarding against threats that pop up mid-flight.
To put it simply:
Audit: A one-time, pre-launch code checkup.
Monitoring: Continuous, live security once you're up and running.
You absolutely need both. An audit makes sure you're starting with a rock-solid foundation, and monitoring keeps you safe for the entire journey.
Do I Need to Be a Tech Wizard to Use Monitoring?
Not at all. While the most powerful, hands-on monitoring tools are definitely built for developers and security pros, you absolutely don't need a computer science degree to get the benefits. The best DeFi platforms are making top-tier security simple and accessible for everyone.
For example, automated platforms like Yield Seeker build sophisticated smart contract monitoring right into their DNA. Our AI agents are the ones doing the heavy lifting—watching protocol health, analyzing risks, and moving capital around—all behind the scenes.
This means that as a user, you get all the protection of 24/7, real-time monitoring without ever having to set up an alert or stare at on-chain data. It’s a huge step in making DeFi security available to everyone, from crypto veterans to total beginners. The security is built right in, not bolted on as an afterthought.
Ready to let AI-powered monitoring and automated yield go to work for you? Yield Seeker makes it simple to earn on your stablecoins with confidence. Get started in minutes and let our AI agents handle the rest.